What You Need To Know About Email Spoofing
New emails fill your inbox daily — some are actually from people you know and trust, while others are from impersonators or extortionists and may contain malware-filled attachments. Many scammers use a "spoofed" email account to appear to be somebody you know rather than a fraudster 6,000 miles away. They might even send an email that appears to be from your own account. Knowing how to spot an email name spoofing is critical to your security.
We'll go over all you need to know — including what email spoofing is and how you can protect yourself from it.
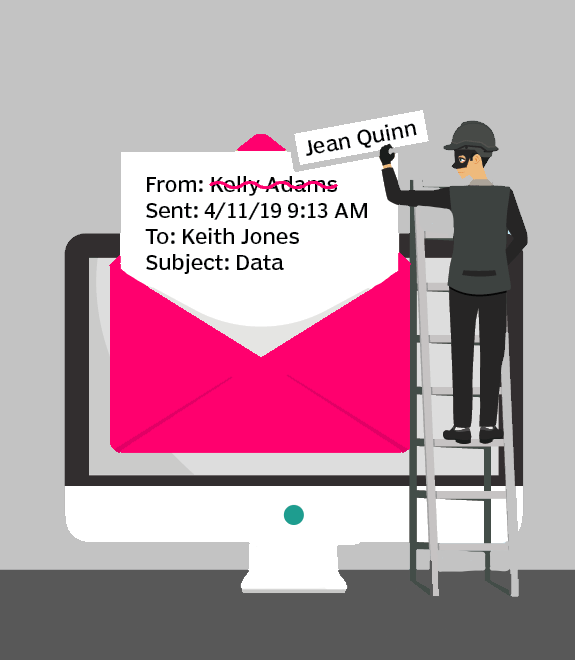
Email Spoofing. What Is It?
In order to get unauthorized access to personal devices or network systems, cybercriminals use email spoofing. When using this tactic, the sender modifies the email header’s “From” address, so the email appears to have been sent from a real, trusted address.
Spammers can now use software to impersonate trusted entities like banks or governments, making detection more difficult. These approaches may lead you to open a malicious attachment or click on a suspicious link.
Email spoofing can be divided into the two categories listed below.
-
Emails that pretend to be someone else
This frequent type of fraud starts with a bogus email. The email appears to be from a person or agency you know and trust. A scammer can send you an email from your bank's fraud department or seemingly from your life insurance company. Or, a company you recently purchased from may have sent you an email confirming your transaction or delivery.
-
Emails that look like they're from a brand company
These emails are meant to mislead recipients into believing that they are getting a legitimate message. You might get an email from a corporation that you've never worked with but is well-known in the field — perhaps an email from a lead generation firm you've expressed an interest in.
How To Protect Yourself?
What to do if an email is spoofed? There are several strategies you can follow to avoid email spoofing.
1. Look at email headers for tell-tale signs. The email headers contain tracking data, and email clients display these headers differently. The tips below will help you spot a fake email header.
-
Make sure the “From” email address matches the display name. If you analyze the email headers, you may find that the email address and the display name don’t match.
-
Verify the “Reply-To” header matches the source. On occasion, the sender will overlook this when responding to a message. If the reply-to address does not match the sender or the site, it is likely a fake.
-
Look for a Return-Path. This shows the source of the email. Although rare, it is possible to alter the Return-path in a message header.
2. Another simple way to check is to click on the three dots on the open email and select “Show Original.”
This will open up a page that gives you a few more details.
If the email contains special characters like support@nd–emià73j.com, you know it’s a phishing attempt. Scroll down further to ensure that the received and received SPF addresses match.
3. Secure email gateway setup. Email security gateways protect businesses by rejecting emails that include suspicious content or do not meet the company's security standards. All gateways detect most malware, spam, and phishing attempts
4. Use anti-malware software. While some software can block advertisements on your YouTube videos, some anti-malware software can spot suspicious websites and block them for you. This avoids spoofing attempts and fake emails.
5. Encrypt your emails for security. A hacker will have a harder time getting their hands on vital information in your emails if you use email encryption. Message-level encryption and Transport Layer Security (TLS) can be used to encrypt both the message and the channel used to deliver it to the recipient.
6. Use secure email. Infrastructure-based email security techniques help reduce attacks and you can stop spoofing email from self. In addition to SMTP (Simple Mail Transfer Protocol) and SPF (Sender Policy Framework), businesses can use DKIM to provide a digital signature layer of security.
-
SMTP is an internet standard communication mechanism for sending and receiving electronic mail by mail servers and other message transfer agents.
-
SPF, on the other hand, lets email senders specify which IP addresses are permitted to send mail for a specific domain.
-
DKIM gives an encryption key and digital signature that ensures the email message has not been tampered with.
7. Get a DMARC record. DMARC (Domain-based Message Authentication, Reporting, and Conformance) can specify what happens if SPF or DKIM fails. Furthermore, hackers are less likely to try to impersonate you if they see your DMARC record. You can learn how your email domain is used and avoid the question, “how to stop someone spoofing my email.
8. Use reverse IP lookups to verify senders. A reverse IP lookup verifies the email's source by locating the IP address's domain name. After that, users can look into who owns the IP address. They can also perform a forward-confirmed reverse Domain Name System (DNS) verification to see if the domain name and server owner relationship is valid. While this isn't always exhaustive, it can be sufficient to strengthen whitelisting techniques. Hackers who employ faked domain records in their bots frequently fail to pass forward validation.
9. Watch out for bogus email addresses. Users' email addresses are typically predictable and well-known. Individuals can learn to avoid responding to emails from unknown or strange senders. Attackers often utilize the same tactics; therefore, users must be cautious.
10. Don’t divulge information. Fake emails normally only cause big issues once the receiver responds with personal data. To reduce the risk of email spoofing, never send personal information in emails.
11. Avoid unexpected attachments and links. Check every part of an email for warning signs like misspellings and odd file extensions before opening a link or attachment.
Conclusion
There are numerous methods to make sure that an email sender is trustworthy. Educating ourselves on these methods and enforcing them for our safety should be a priority. Even a single attack can result in identity theft, business disruption, reputation harm, and multi-million dollar losses.
Now that you know how to protect yourself from such attacks, stay safe online.

